The Infrastructure Behind Travel eSIMs
You know what’s funny about travel eSIMs?
We talk about them like they’re an app. Scan QR. Install. Boom, you’re online in Tokyo before your jet lag even arrives.
But under that “boom” is a stack of infrastructure that is way closer to banking security than travel marketing. Provisioning standards. Certificate chains. Secure elements. Remote lifecycle rules. The stuff that makes eSIM work at scale without turning into chaos.
And because nobody explains it, a lot of people assume eSIM is basically “a digital SIM card you download”.
It is, but the important part is how it’s allowed to be downloaded, who is trusted to deliver it, and what happens to that profile after it’s on your device.
Let’s demystify it without turning this into a telecom lecture.
Provisioning standards
An eSIM is not just “a SIM, but invisible”. It’s a system defined by GSMA specifications, so operators, device makers, and subscription management platforms can all speak the same language.
For consumer devices, the remote SIM provisioning flow is built around a few key actors:
Who does what
- eUICC (the eSIM chip): the secure hardware on your device that stores one or more operator profiles.
- LPA (Local Profile Assistant): the “manager” on your phone that requests, downloads, and installs profiles.
- SM-DP+ (Subscription Manager Data Preparation Plus): the backend that prepares and securely delivers the operator profile to your device.
This is why travel connectivity is not only about “coverage”. It’s about whether the provisioning plumbing is compliant, interoperable, and trusted.
Because if the plumbing is messy, everything else becomes fragile: installs fail, activations break, profiles get stuck, or support becomes a human-driven nightmare.
Certificate chains
Here’s the part most people never hear: the remote provisioning ecosystem relies on GSMA public key infrastructure (PKI). In normal human language, that means a trust system based on certificates, so the device and the provisioning servers can authenticate each other and securely exchange profiles.
Think of it like this:
Your eSIM chip will not accept just any “profile file” from the internet. It needs cryptographic proof that the entity delivering it is legitimate within the GSMA ecosystem. That legitimacy is established through certificates and certificate issuers, rooted in GSMA-defined trust.
This is why the serious eSIM world cares about boring phrases like “certificate issuer” and “trusted root”. If those are compromised or poorly managed, the entire idea of secure remote provisioning collapses.
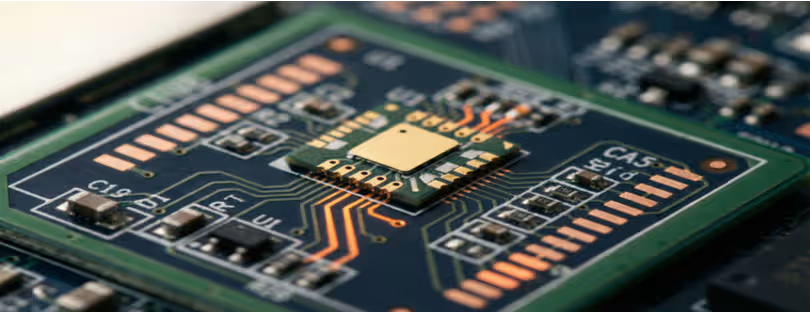
Secure elements
The eUICC is literally a secure element: specialized hardware designed to protect sensitive credentials and run security-critical operations. That’s the whole point. It is built so that the subscription identity and keys are protected even if the rest of the device is compromised.
It’s also why the eSIM supply chain is audited and accredited. GSMA runs a Security Accreditation Scheme (SAS), with standardized audits for eUICC suppliers and subscription management providers.
So when someone says “eSIM is just software”, the correct response is: the user experience is software. The trust anchor is hardware plus audited processes.
Remote profile lifecycle
A lot of people think eSIM ends at install.
In reality, the profile has a lifecycle: download, install, enable, disable, delete. These aren’t “nice-to-haves”. They’re how the system stays manageable when you have millions of devices, multiple operators, and constant travel.
And this lifecycle matters in travel more than you’d think:
Where lifecycle show up in real travel life
- You install an eSIM too early, then want to disable it until you land.
- You switch countries mid-trip and want to add a second profile.
- You finish a trip and want to delete a profile so your list doesn’t become a museum of past vacations.
- A business traveler needs a clean separation between corporate connectivity and personal use, and lifecycle control makes that possible.
Also, the industry is evolving: GSMA’s work on IoT eSIM provisioning (like SGP.32) exists because not every device has a nice touchscreen UI to scan QR codes, and remote management needs to scale differently. That matters for travel tech too, because travel is full of “quiet connectivity” devices: trackers, kiosks, payment terminals, luggage tech.
So yes, travel connectivity has an infrastructure layer. It’s just invisible when it works.
And when it doesn’t, you suddenly learn what an SM-DP+ is at 2am in an airport.
The hidden economics of “unlimited” eSIM plans
Now let’s talk about the other thing everyone argues about loudly, while missing the real mechanism.
Unlimited.
Not “unlimited (but actually 1GB/day)”, not “unlimited (but streaming is capped)”, not “unlimited (but hotspot is basically illegal)”.
Just… unlimited.
Here’s the truth: unlimited is usually not a promise. It’s a pricing strategy designed to control margin risk.
And the reason isn’t throttling as a concept. It’s cost exposure.
Wholesale cost exposure
Every gigabyte has a cost somewhere in the chain. Even when you buy a travel eSIM from a shiny app, the underlying connectivity still touches wholesale arrangements, roaming settlement, and network-to-network charging mechanics. GSMA’s wholesale frameworks and settlement processes exist precisely because operators charge each other for usage.
Inside the EU, regulators publish data showing wholesale caps and actual wholesale prices under roaming regulation. The key idea is simple: wholesale pricing moves, and it directly affects the economics of “I can give everyone unlimited data”.
Now zoom out beyond the EU, and wholesale exposure can vary wildly depending on destination, partner networks, and commercial terms. That is the part most “unlimited” marketing never mentions, because it’s not sexy. It’s finance.
So if you’re a provider selling “unlimited”, you have a problem to solve: how do you cap your cost without capping your marketing?
You do it with policy.
Traffic shaping
Traffic shaping is the polite name for “we treat different traffic differently”.
Sometimes it’s speed tiers. Sometimes it’s deprioritisation. Sometimes it’s video optimization. Sometimes it’s hidden rules that kick in when the network is busy.
Modern mobile networks can enforce policies in the core network and user plane, and DPI is one technique used to classify and manage traffic. In 5G contexts, DPI is often discussed as being implemented around the user plane functions that handle user data forwarding.
That doesn’t mean every travel eSIM is doing a deep inspection of everything you do. It means the technical capability to enforce policy at a granular level exists, and it’s part of how operators and connectivity platforms manage cost and performance tradeoffs.
Fair usage thresholds
Fair usage is basically the “contractual story” that sits on top of the cost model.
You get a chunk of high-speed data, then the service continues at reduced speed, or under different priority rules. Many providers explain this as FUP, even if users only notice it as “it got slow”.
From a consumer fairness perspective, even advertising regulators have guidance: “unlimited” claims can be acceptable if significant limitations are clearly explained. Translation: if you say unlimited, you still need to be honest about the rules that materially change the experience.
And here’s the key: fair usage is rarely about punishing “bad users”.
It’s usually margin insurance.
If 5 percent of users can burn through a disproportionate share of data, unlimited pricing collapses unless you have thresholds.
Why “unlimited” is often margin insurance
So the economics looks like this:
Why providers love unlimited messaging
- It reduces decision fatigue. People buy faster.
- It compresses price competition into a single word.
- It lets the provider predict revenue while controlling variable costs through policy.
And that last part is the whole game.
Because the provider cannot fully control what you do, but they can control how the network treats what you do after you cross a threshold.
That’s not inherently evil. It’s how the system stays viable.
The problem is when the rules are hidden, vague, or framed like a magic trick.
Final thoughts – A better way to judge travel connectivity in 2026
If you take one thing from all this, make it this:
Travel connectivity is no longer just a product category. It’s an infrastructure stack plus an economic model.
On the infrastructure side, the industry is standardizing and hardening the provisioning ecosystem with GSMA specs, PKI trust chains, and audited security regimes, and it is expanding provisioning models to handle IoT-style realities too.
On the economics side, “unlimited” is increasingly a packaging layer designed to manage wholesale exposure, settlement realities, and unpredictable usage patterns, and that pushes providers toward policy control like fair usage thresholds and traffic management.
So when you compare players in the market, do not only ask “how many countries” and “how cheap”.
Ask two better questions:
- How mature is their provisioning and lifecycle stack, and how well does it behave when things go wrong?
- How transparent is their economic model, especially when they sell “unlimited”?
The trendline is clear: the winners will not just be the loudest marketers. They’ll be the ones building trustworthy infrastructure and pricing that survives contact with real-world roaming economics.