5 major US carriers vulnerable to SIM-swapping tactics, study
A Princeton study (PDF) has discovered that five US prepaid carriers use authentication techniques that are vulnerable to SIM-swapping tactics. The researchers signed up for 10 prepaid accounts each on AT&T, T-Mobile, Tracfone, US Mobile and Verizon Wireless for a total of 50.
They found that they only needed to successfully answer one thing to verify their identity and get the companies to switch their service to a SIM card they already have. It didn’t even matter if they got the other authentication challenges wrong.
That kind of SIM-swapping technique could be used by attackers to gain control of a victim’s phone number. They can then use that number to reset the victim’s passwords and access, say, their emails and bank accounts.
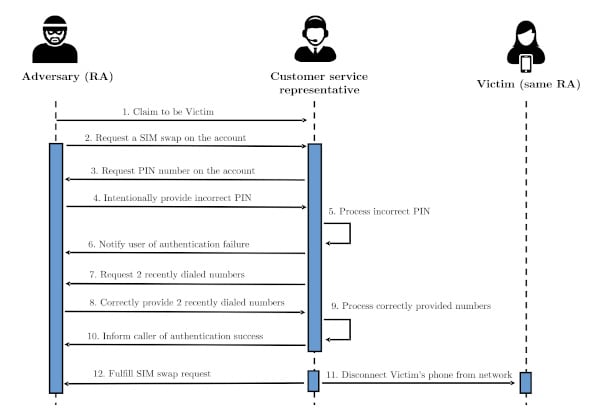
To test the carriers’ security measures, they called the companies to request for a SIM swap and intentionally provided the wrong PIN number to force the customer service rep to try another authentication method. When asked for the account holder’s date of birth or billing ZIP code, they’d say that they must’ve made a mistake upon signup and provided the wrong information.
The customer service rep would then have to move to a third type of authentication method, which is asking the caller for their two most recently made calls. It was through this method that the researchers were successfully able to complete the SIM swaps. And that’s alarming, since attackers can easily trick victims into calling random phone numbers.
For the part of their research that targeted US telcos, the research team said it created 50 prepaid accounts, 10 with each carrier. For each account, the research team used the 50 SIM cards on a unique phone, and for real calls, in order to create a realistic call history.
When the time came, the research team called each telco’s customer support center and applied a similar procedure.
The idea was that the acker calls a telco’s support center to request a SIM card change, but intentionally provides a wrong PIN and account owner details.
“When providing incorrect answers to personal questions such as date of birth or billing ZIP code, would explain that they had been careless at signup, possibly having provided incorrect information, and could not recall the information they had used,” researchers said, explaining the motives they provided to call center staff.
At this point, after failing the first two authentication mechanisms (PIN and account owner details), telco call center operators are required, based on their procedures, to move to a third mechanism during which they ask the account owner to provide details about the last two recently made calls.
The research team says that an attacker could trick a victim into placing calls to specific numbers. For example, a scenario of “you won a prize; call here; sorry, wrong number; call here instead.”
After the attacker has tricked the SIM card owner into placing those two calls, they can use these details to call the telco’s call center and carry out a SIM swap.
Princeton researchers said they were able to trick all five US prepaid wireless carriers using this scenario.
When they published their research yesterday, four providers were still using the vulnerable procedure, despite the research team notifying all the affected parties. Of the five, T-Mobile told the research team they discontinued the use of call logs for customer authentication after reviewing their research.
In addition, the researchers examined 140 popular online sites and services that use phone authentication to see what attackers can do with the numbers they hijack. They were easily able to reset passwords on 17 of those services using only the hijacked SIMs, since they weren’t asked additional authentication questions.