The Infrastructure Behind Travel Connectivity
Open any travel eSIM app, and it feels simple: pick a country, pay, scan a QR, and you are online. But that clean checkout flow hides a surprisingly dense stack of infrastructure that has to work perfectly across borders, networks, devices, and security domains.
And here’s the part most travelers never hear: a lot of what determines whether your “instant eSIM” actually works has nothing to do with the brand name on the app. It depends on provisioning rails, security accreditation, discovery services, roaming interconnect, and a set of standards that were designed to keep the whole system interoperable and tamper-resistant.
If you read Alertify, you already know the travel connectivity market looks crowded on the surface. Underneath, the pipes are far more concentrated and far more standardized than the marketing suggests.
The quiet core: remote provisioning
Let’s start with the most important hidden layer: Remote SIM Provisioning (RSP). For consumer devices, the GSMA’s SGP.22 architecture defines how eSIM profiles are prepared, delivered, installed, enabled, disabled, and deleted on a device.
Two pieces matter a lot in practice:
SM-DP+
This is the Subscription Manager Data Preparation+ component. In plain language, it is the system that packages an operator profile and securely delivers it to your device. If your download fails, stalls, or keeps looping, this layer is often involved.
SM-DS
This is the Subscription Manager Discovery Server. It helps a device discover where to fetch profiles from, depending on the flow being used. It is not the “app,” but it can decide whether your app experience is smooth or painful.
This is why two different travel eSIM brands can feel identical during installation, or fail in suspiciously similar ways during peak travel periods. They may be riding the same RSP back-end patterns.
The security layer people assume “just exists”
Every time someone says, “eSIM is safer because it’s embedded,” they are gesturing toward real security properties, but skipping the mechanics.
An eUICC is a secure element that can store one or more operator profiles and enforce security controls around them. In the EU context, ENISA describes eUICC as an embedded secure element that holds subscription profiles and is central to safeguarding security for both customer and operator.
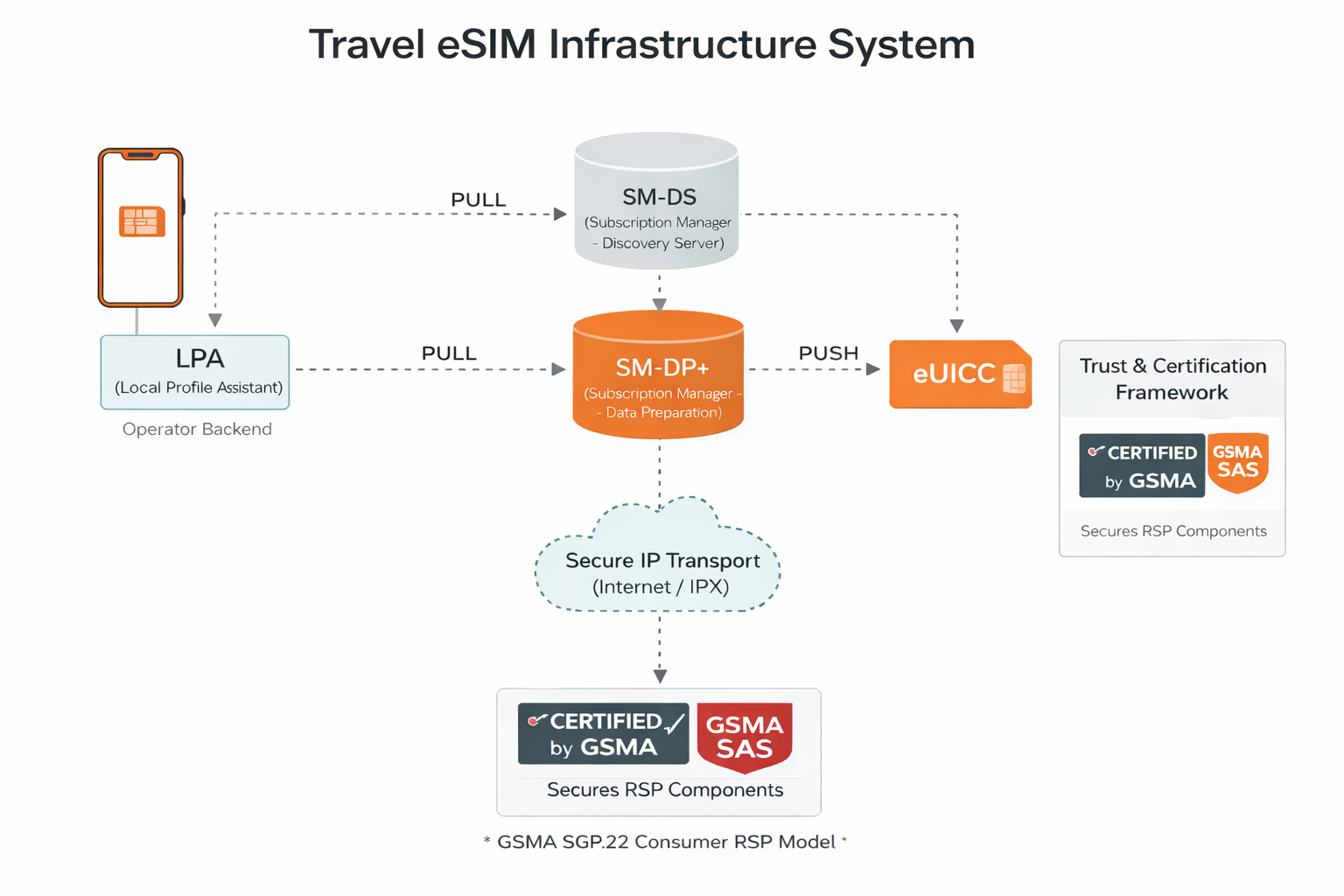
GSMA SAS
The GSMA Security Accreditation Scheme (SAS) is built around standardized security audits, including for eUICC/UICC production and for subscription management service providers. That matters because provisioning platforms handle very sensitive assets.
So when a provider says they are “secure,” what you actually want to know is whether their ecosystem (or the ecosystem they rely on) aligns with recognized accreditation and audit frameworks.
Why “coverage” is not just a map
Travel eSIM marketing makes coverage look like geography. The infrastructure view makes it look like routing, interconnect, and policy.
Even if you buy a plan for “Spain,” your traffic still needs to traverse roaming interconnect pathways between networks. Historically, GRX was used as a hub model for mobile data roaming interconnect, reducing the need for every operator to build point-to-point links with every other operator.
Today, IPX is commonly discussed as the evolution of that concept for IP-based interconnect services. Operators and large connectivity players run IPX platforms that support roaming signaling and data roaming connectivity over managed global backbones.
If this layer is congested, misconfigured, or negotiated poorly, the “same” eSIM plan can feel fast on one day and sluggish on another. It can also explain weird edge cases where the phone shows bars, but the session behaves like it is stuck behind invisible walls.
The device side: your phone is part of the system
Most people talk about eSIM like it is a file you download. In reality, your device is an active security and entitlement participant.
On consumer phones, the local profile assistant (often referred to as the LPA in industry discussions) is responsible for orchestrating the user-side of provisioning interactions with the eUICC and the provisioning servers. The OS implementation matters. Small differences in how devices handle retries, timeouts, or network changes can translate into “this provider is bad” when the real issue is a fragile edge case on a specific device model or OS build.
This is also why support quality is so uneven across the travel eSIM market. Front-end brands can be excellent at content and pricing, but still struggle to debug failures that originate in deep infrastructure layers they do not directly control.
IoT standards are reshaping expectations for everyone
Even if you only care about travel, you should pay attention to SGP.32, because it reflects where the industry is heading: more automation, less user interface dependency, more lifecycle management.
The GSMA positions SGP.32 as an eSIM IoT architecture and requirements track, designed for constrained devices and long-lived deployments.
What does that have to do with travel? It is pushing the market toward a clearer separation between “the connectivity control plane” and “the retail packaging.” As more infrastructure becomes standardized and API-driven, the market naturally produces more brands on top of fewer core rails.
That trend is already visible in the travel eSIM ecosystem: a growing number of storefronts, while the underlying provisioning, discovery, and wholesale connectivity layers consolidate around a smaller set of enablers and platforms.
The uncomfortable truth: most brands are not differentiated at the infrastructure layer
This is the moment where some readers expect a dramatic takedown. Not needed. The reality is more practical than that.
Many travel eSIM brands differentiate on:
- Distribution (affiliates, airlines, OTAs, influencers)
- UX and onboarding
- Plan packaging, pricing psychology, and promo strategy
- Support responsiveness and refund handling
- Clarity (or lack of it) around speed limits, tethering, and fair usage
But at the deepest infrastructure level, a lot of the market is using similar architectural building blocks because the ecosystem is standards-driven. That is not “bad.” It is how global interoperability works. It also means your editorial job (and mine) is to help readers understand what actually matters when everything looks the same on the surface.
What to look for as a buyer
If you want a practical checklist that maps to the infrastructure reality:
- Does the provider clearly explain activation and troubleshooting steps that match modern RSP flows (not vague “restart your phone” advice)?
- Do they disclose network partners where possible, or at least set realistic expectations about performance variability?
- Do they describe speed policies, throttling, tethering, and “unlimited” logic in a way that feels operationally honest?
- Do they have support that can handle provisioning failures without blaming the user?
Those are not marketing questions. They are proxy signals for how mature their operational stack is.
Conclusion
The travel connectivity market keeps selling “simplicity,” but the real story is that simplicity is manufactured by infrastructure: GSMA-defined provisioning architectures like SGP.22, evolving standards like SGP.32, security accreditation regimes like SAS, and roaming interconnect foundations like GRX and IPX.
And that leads to a clean conclusion you can actually use: the next competitive battleground is not who can launch the 200th “best eSIM for Italy” landing page. It is who can earn trust by being transparent about the operational realities of these rails, and who can build a support and product layer that respects how the infrastructure truly behaves.
In other words, the winners will look less like “a travel eSIM shop” and more like connectivity operators in media clothing: setting expectations, explaining constraints, and turning invisible infrastructure into a predictable experience.